|
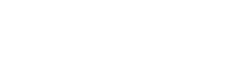
Given that Amazon GuardDuty released in 2017, GuardDuty has been able of examining tens of billions of situations for each moment across many AWS information resources, these kinds of as AWS CloudTrail occasion logs, Amazon Digital Non-public Cloud (Amazon VPC) Stream Logs, and DNS query logs, Amazon Straightforward Storage Provider (Amazon S3) information aircraft gatherings, Amazon Elastic Kubernetes Provider (Amazon EKS) audit logs, and Amazon Relational Databases Service (Amazon RDS) login activities to shield your AWS accounts and methods.
In 2020, GuardDuty extra Amazon S3 defense to consistently keep an eye on and profile S3 details accessibility situations and configurations to detect suspicious pursuits in Amazon S3. Very last year, GuardDuty launched Amazon EKS security to watch handle plane action by examining Kubernetes audit logs from existing and new EKS clusters in your accounts, Amazon EBS malware defense to scan destructive information residing on an EC2 instance or container workload making use of EBS volumes, and Amazon RDS security to recognize prospective threats to information saved in Amazon Aurora databases—recently generally obtainable.
GuardDuty brings together machine discovering (ML), anomaly detection, network checking, and destructive file discovery employing different AWS details resources. When threats are detected, GuardDuty mechanically sends security conclusions to AWS Safety Hub, Amazon EventBridge, and Amazon Detective. These integrations assist centralize monitoring for AWS and husband or wife products and services, automate responses to malware conclusions, and complete stability investigations from GuardDuty.
These days, we are announcing the common availability of Amazon GuardDuty EKS Runtime Monitoring to detect runtime threats from about 30 stability findings to shield your EKS clusters. The new EKS Runtime Monitoring employs a thoroughly managed EKS add-on that provides visibility into particular person container runtime pursuits, these as file access, system execution, and community connections.
GuardDuty can now discover particular containers within just your EKS clusters that are probably compromised and detect tries to escalate privileges from an unique container to the fundamental Amazon EC2 host and the broader AWS surroundings. GuardDuty EKS Runtime Monitoring conclusions provide metadata context to identify opportunity threats and incorporate them just before they escalate.
Configure EKS Runtime Checking in GuardDuty
To get started, very first enable EKS Runtime Monitoring with just a number of clicks in the GuardDuty console.

Once you permit EKS Runtime Checking, GuardDuty can commence monitoring and analyzing the runtime-exercise functions for all the existing and new EKS clusters for your accounts. If you want GuardDuty to deploy and update the essential EKS-managed add-on for all the present and new EKS clusters in your account, opt for Control agent routinely. This will also produce a VPC endpoint by way of which the stability agent delivers the runtime events to GuardDuty.
If you configure EKS Audit Log Monitoring and runtime checking with each other, you can realize ideal EKS safety each at the cluster management aircraft degree, and down to the personal pod or container operating procedure level. When utilised together, risk detection will be more contextual to allow for fast prioritization and reaction. For example, a runtime-primarily based detection on a pod exhibiting suspicious behavior can be augmented by an audit log-dependent detection, indicating the pod was unusually introduced with elevated privileges.
These possibilities are default, but they are configurable, and you can uncheck just one of the packing containers in order to disable EKS Runtime Checking. When you disable EKS Runtime Monitoring, GuardDuty instantly stops checking and analyzing the runtime-action gatherings for all the present EKS clusters. If you experienced configured automated agent administration as a result of GuardDuty, this motion also gets rid of the security agent that GuardDuty had deployed.
To study more, see Configuring EKS Runtime Checking in the AWS documentation.
Take care of GuardDuty Agent Manually
If you want to manually deploy and update the EKS managed insert-on, such as the GuardDuty agent, for every cluster in your account, uncheck Handle agent routinely in the EKS defense configuration.
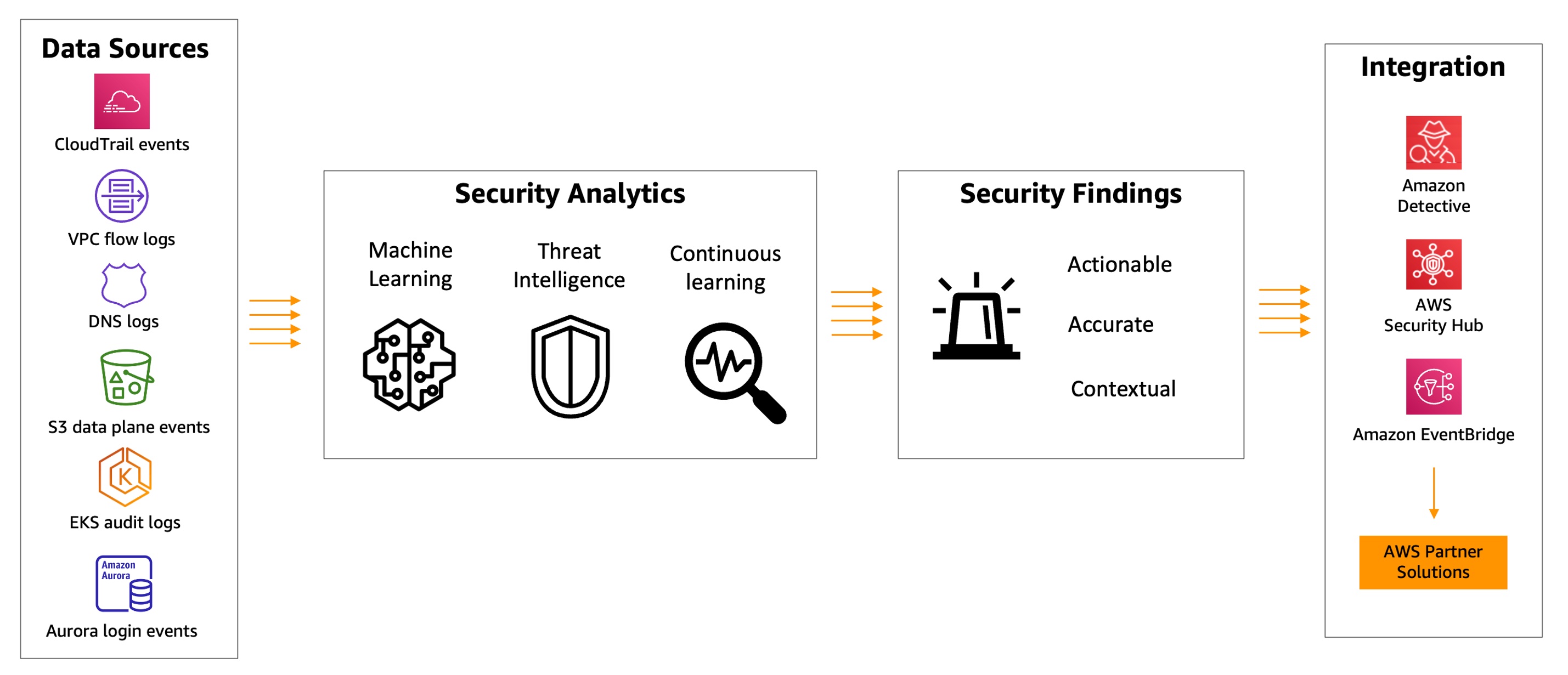
When controlling the increase-on manually, you are also dependable for developing the VPC endpoint through which the security agent delivers the runtime functions to GuardDuty. In the VPC endpoint console, select Create endpoint. In the phase, choose Other endpoint products and services for Services category, enter com.amazonaws.us-east-1.guardduty-details for Company name in the US East (N. Virginia) Location, and opt for Confirm services.
Right after the services title is correctly verified, decide on VPC and subnets where your EKS cluster resides. Less than Supplemental settings, pick out Help DNS name. Under Stability teams, pick a stability group that has the in-bound port 443 enabled from your VPC (or your EKS cluster).
Insert the next plan to limit VPC endpoint use to the specified account only:
"Model": "2012-10-17",
"Assertion": [
"Action": "*",
"Resource": "*",
"Effect": "Allow",
"Principal": "*"
,
"Condition":
"StringNotEquals":
"aws:PrincipalAccount": "123456789012"
,
"Action": "*",
"Resource": "*",
"Effect": "Deny",
"Principal": "*"
]
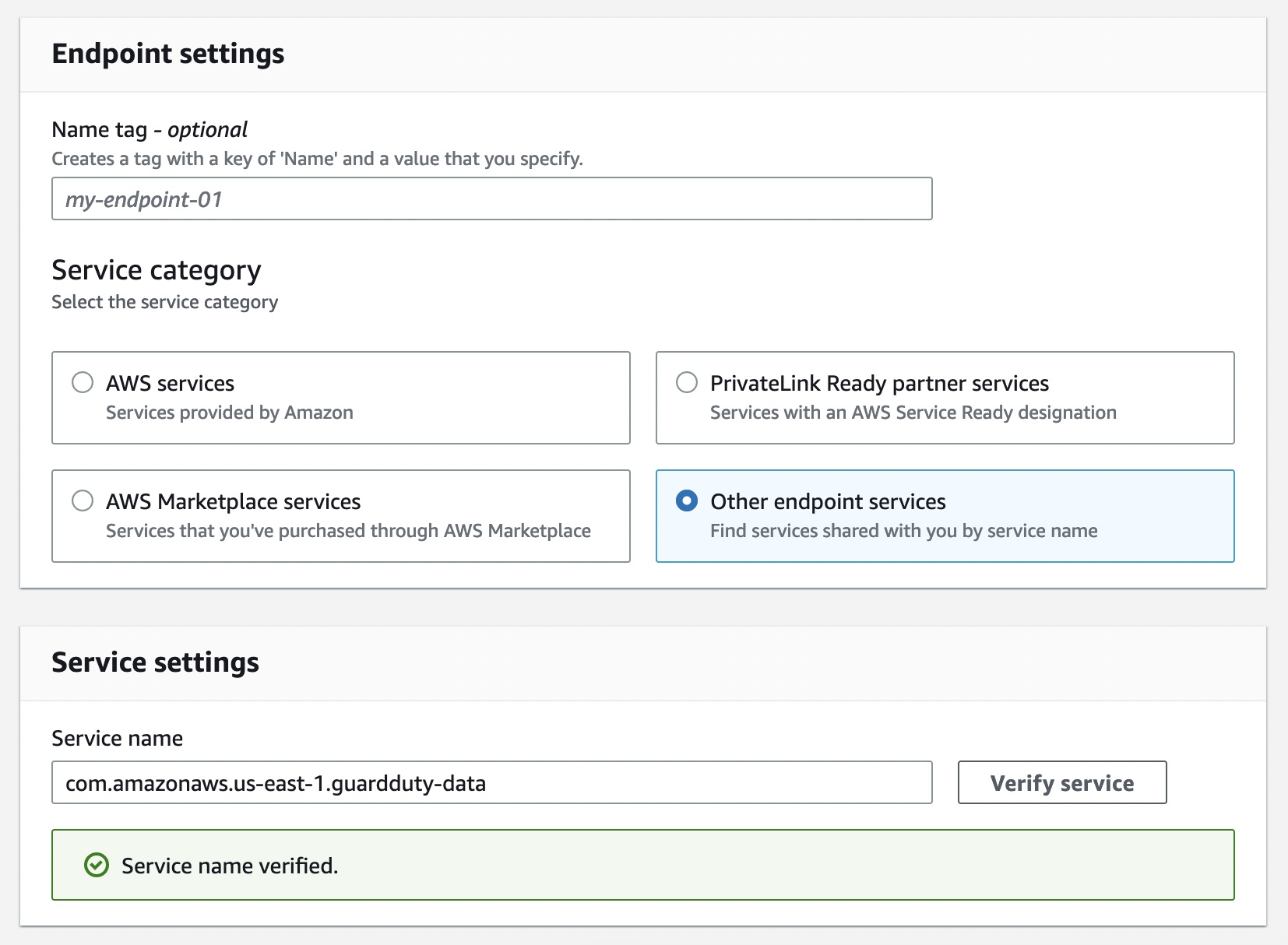
Now, you can set up the Amazon GuardDuty EKS Runtime Checking insert-on for your EKS clusters. Pick out this include-on in the Increase-ons tab in your EKS cluster profile on the Amazon EKS console.
When you allow EKS Runtime Checking in GuardDuty and deploy the Amazon EKS add-on for your EKS cluster, you can look at the new pods with the prefix aws-guardduty-agent. GuardDuty now commences to consume runtime-exercise functions from all EC2 hosts and containers in the cluster. GuardDuty then analyzes these activities for prospective threats.
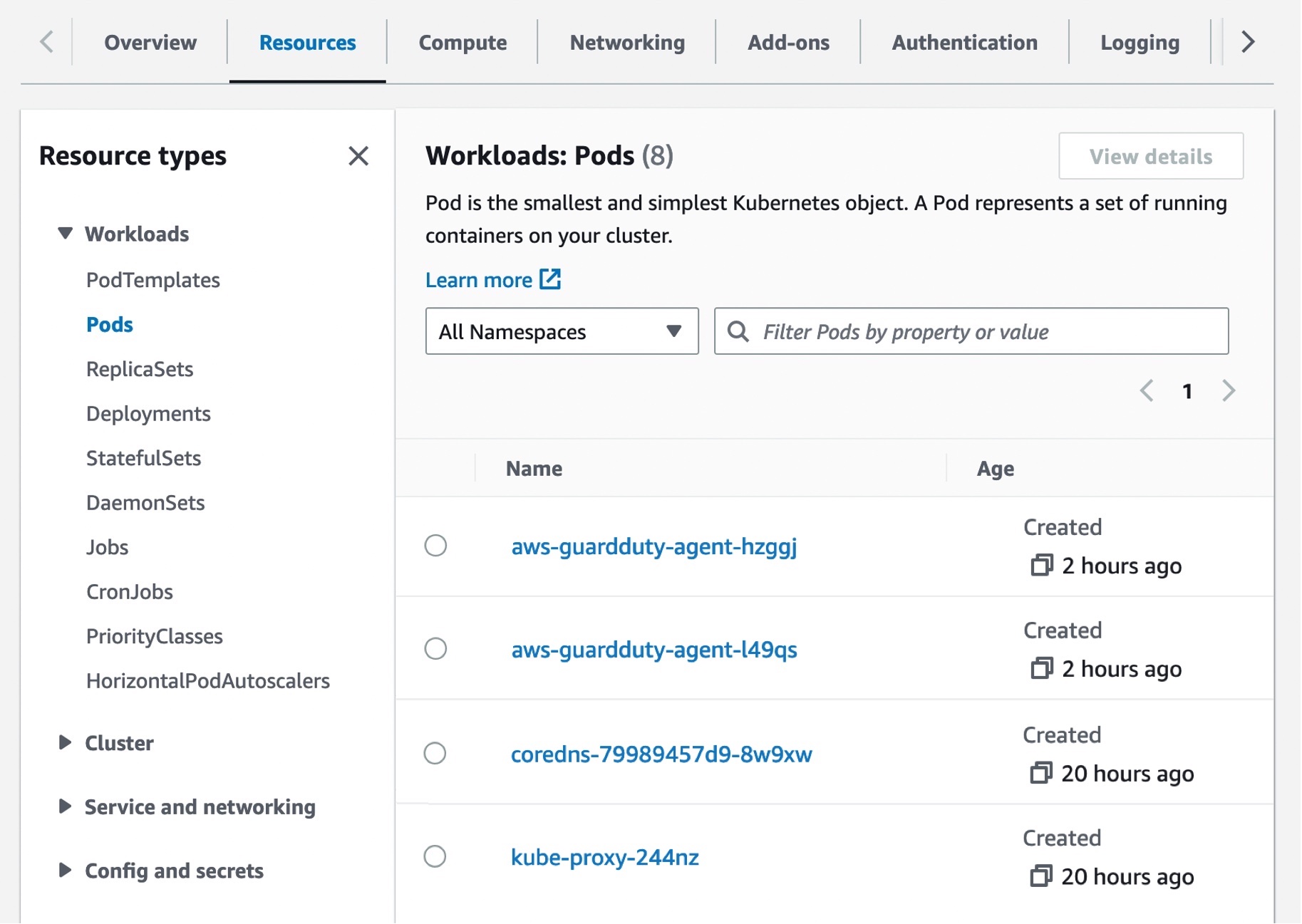
These pods accumulate different party forms and deliver them to the GuardDuty backend for threat detection and assessment. When controlling the increase-on manually, you require to go through these ways for each individual EKS cluster that you want to keep an eye on, which includes new EKS clusters.
To master a lot more, see Handling GuardDuty agent manually in the AWS documentation.
Checkout EKS Runtime Safety Conclusions
When GuardDuty detects a possible threat and generates a stability discovering, you can look at the details of the corresponding conclusions. These stability findings indicate either a compromised EC2 occasion, container workload, an EKS cluster, or a set of compromised qualifications in your AWS setting.
If you want to create EKS Runtime Checking sample findings for tests functions, see Producing sample findings in GuardDuty in the AWS documentation. Here is an instance of prospective safety issues: a recently established or not long ago modified binary file in an EKS cluster has been executed.

The ResourceType for an EKS Protection locating type could be an Instance, EKSCluster, or Container. If the Source kind in the finding specifics is EKSCluster, it indicates that possibly a pod or a container within an EKS cluster is likely compromised. Depending on the potentially compromised resource kind, the finding aspects may perhaps contain Kubernetes workload details, EKS cluster aspects, or occasion particulars.

The Runtime details this sort of as method specifics and any expected context explain details about the noticed procedure, and the runtime context describes any extra data about the likely suspicious action.

To remediate a compromised pod or container image, see Remediating EKS Runtime Checking findings in the AWS documentation. This document describes the recommended remediation measures for every useful resource form. To master far more about stability finding styles, see GuardDuty EKS Runtime Monitoring getting kinds in the AWS documentation.
Now Accessible
You can now use Amazon GuardDuty for EKS Runtime Monitoring. For a complete record of Areas wherever EKS Runtime Monitoring is accessible, visit area-distinct element availability.
The initially 30 days of GuardDuty for EKS Runtime Checking are available at no further demand for present GuardDuty accounts. If you enabled GuardDuty for the first time, EKS Runtime Checking is not enabled by default, and demands to be enabled as described previously mentioned. Following the trial time period finishes in the GuardDuty, you can see the approximated price of EKS Runtime Monitoring. To learn much more, see the GuardDuty pricing website page.
For extra data, see the Amazon GuardDuty Consumer Guide and mail opinions to AWS re:Article for Amazon GuardDuty or by way of your usual AWS help contacts.
– Channy