|
At AWS, security is the leading priority. Beginning now, Amazon Very simple Storage Support (Amazon S3) encrypts all new objects by default. Now, S3 instantly applies server-aspect encryption (SSE-S3) for each and every new object, unless of course you specify a diverse encryption possibility. SSE-S3 was 1st launched in 2011. As Jeff wrote at the time: “Amazon S3 server-facet encryption handles all encryption, decryption, and vital administration in a thoroughly clear vogue. When you Place an object, we make a distinctive crucial, encrypt your data with the vital, and then encrypt the essential with a [root] key.”
This transform puts yet another security most effective apply into result automatically—with no impact on general performance and no action necessary on your side. S3 buckets that do not use default encryption will now quickly apply SSE-S3 as the default placing. Existing buckets presently making use of S3 default encryption will not adjust.
As always, you can opt for to encrypt your objects applying a single of the three encryption choices we offer: S3 default encryption (SSE-S3, the new default), shopper-provided encryption keys (SSE-C), or AWS Essential Administration Service keys (SSE-KMS). To have an extra layer of encryption, you could also encrypt objects on the consumer side, working with shopper libraries this kind of as the Amazon S3 encryption consumer.
When it was very simple to permit, the opt-in nature of SSE-S3 meant that you had to be certain that it was constantly configured on new buckets and confirm that it remained configured effectively in excess of time. For organizations that demand all their objects to keep on being encrypted at rest with SSE-S3, this update allows meet up with their encryption compliance necessities devoid of any extra tools or consumer configuration variations.
With today’s announcement, we have now produced it “zero click” for you to apply this foundation amount of encryption on just about every S3 bucket.
Confirm Your Objects Are Encrypted
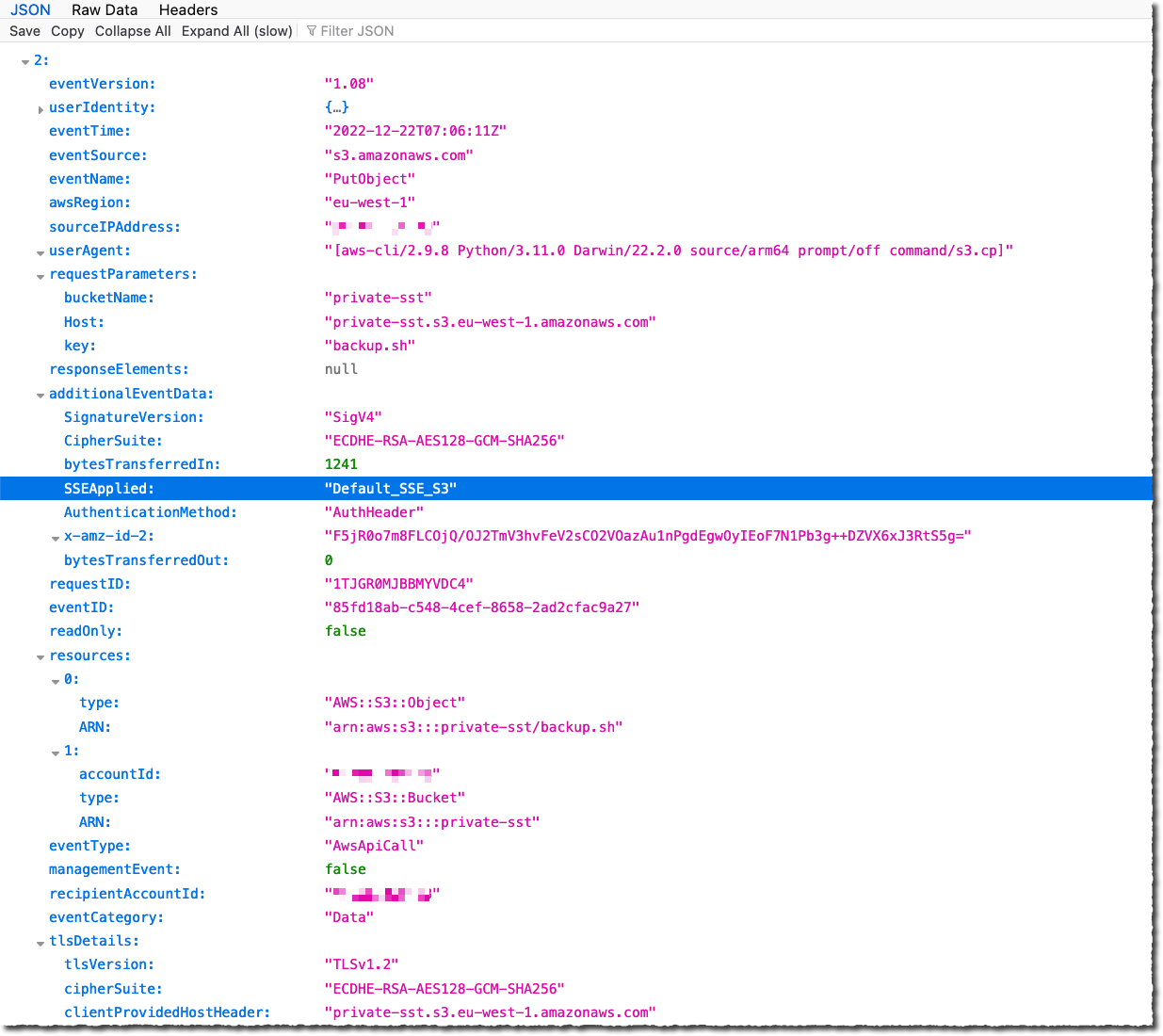
The change is seen nowadays in AWS CloudTrail information event logs. You will see the adjustments in the S3 segment of the AWS Management Console, Amazon S3 Stock, Amazon S3 Storage Lens, and as an added header in the AWS CLI and in the AWS SDKs in excess of the upcoming handful of months. We will update this blog site article and documentation when the encryption status is available in these tools in all AWS Areas.
To confirm the transform is powerful on your buckets right now, you can configure CloudTrail to log data events. By default, trails do not log knowledge activities, and there is an more cost to help it. Facts functions clearly show the useful resource functions done on or in just a source, these as when a user uploads a file to an S3 bucket. You can log details activities for Amazon S3 buckets, AWS Lambda functions, Amazon DynamoDB tables, or a mix of individuals.
Once enabled, research for PutObject API for file uploads or InitiateMultipartUpload for multipart uploads. When Amazon S3 routinely encrypts an object making use of the default encryption configurations, the log incorporates the next discipline as the title-value pair: "SSEApplied":"Default_SSE_S3". Listed here is an illustration of a CloudTrail log (with details event logging enabled) when I uploaded a file to 1 of my buckets employing the AWS CLI command aws s3 cp backup.sh s3://personal-sst.
Amazon S3 Encryption Choices
As I wrote earlier, SSE-S3 is now the new base stage of encryption when no other encryption-variety is specified. SSE-S3 works by using Advanced Encryption Standard (AES) encryption with 256-little bit keys managed by AWS.
You can decide on to encrypt your objects making use of SSE-C or SSE-KMS alternatively than with SSE-S3, possibly as “one click” default encryption options on the bucket, or for particular person objects in Put requests.
SSE-C allows Amazon S3 accomplish the encryption and decryption of your objects whilst you keep management of the keys utilized to encrypt objects. With SSE-C, you don’t will need to apply or use a shopper-aspect library to execute the encryption and decryption of objects you retailer in Amazon S3, but you do need to take care of the keys that you send to Amazon S3 to encrypt and decrypt objects.
With SSE-KMS, AWS Essential Management Support (AWS KMS) manages your encryption keys. Utilizing AWS KMS to manage your keys delivers many extra benefits. With AWS KMS, there are different permissions for the use of the KMS important, supplying an further layer of manage as well as safety from unauthorized obtain to your objects stored in Amazon S3. AWS KMS supplies an audit trail so you can see who employed your crucial to accessibility which object and when, as well as check out failed attempts to accessibility data from people without permission to decrypt the facts.
When employing an encryption client library, such as the Amazon S3 encryption shopper, you keep control of the keys and complete the encryption and decryption of objects shopper-facet using an encryption library of your alternative. You encrypt the objects right before they are despatched to Amazon S3 for storage. The Java, .Web, Ruby, PHP, Go, and C++ AWS SDKs help consumer-aspect encryption.
You can comply with the directions in this web site publish if you want to retroactively encrypt existing objects in your buckets.
Out there Now
This alter is helpful now, in all AWS Locations, together with on AWS GovCloud (US) and AWS China Locations. There is no further value for default item-level encryption.