Exposed, unfamiliar endpoints on an enterprise’s network are far more than a safety menace they are a brand name liability. This week, Forrester’s Stability and Risk Summit designed a compelling situation for how technology have confidence in is essential to driving manufacturer rely on.
The periods highlighted how an enterprise’s efficiency at bettering its security posture specifically affects gains.
“Because when some thing touches as significantly income as cybersecurity does, it is a main competency. And you simply cannot argue that it is not,” Jeff Pollard, VP and principal analyst at Forrester, told the viewers in the course of a session.
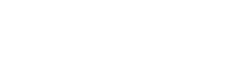
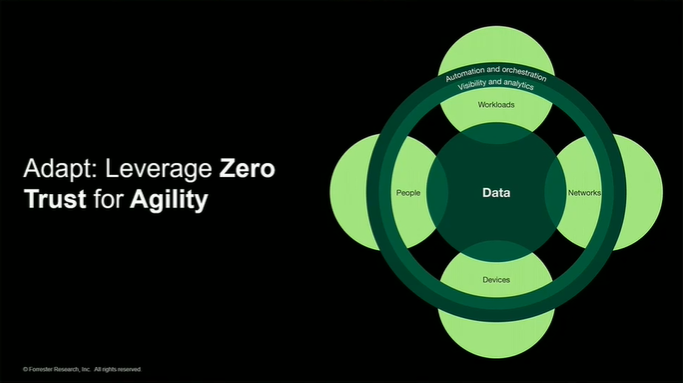
CISOs experience the challenge of consolidating tech stacks although supporting a escalating base of endpoints and identities. Zero-rely on network entry (ZTNA) and zero-trust edge are core to zero-trust frameworks. In addition, zero have confidence in does not have to be high-priced to be efficient, which was a pivotal stage built for the duration of the event.
Zero have faith in will make just about every endpoint extra reliable and agile, enabling enterprises to adapt rapidly to customers’ shifting needs. Resource: Forrester’s Security and Risk Summit, 2022
Allie Mellen, a senior analyst at Forrester, noted during the occasion, “Zero trust goes hand in hand with have faith in. For the reason that what you can do is make sure that all of your devices are safe and protected. And that even in a potential bodily conflict, you ought to shift your complete staff out of the place. Suppose they leave a machine powering,” she said. “You can control that possibility you can wipe that system you can make guaranteed that no one is heading to get access to consumer data on that device.”
Mellen underscored the will need for just about every organization to continue to be agile and adaptive to likely geopolitical hazards.
“This is very significant as you imagine that you may have to shift operations at a moment’s recognize,” she reported.
Securing any where-work endpoints
A session presented by Paddy Harrington, senior analyst at Forrester, highlighted various insights that companies could use to guard their endpoints. CISOs and their teams need to adopt additional powerful cell application management and endpoint management strategies to support anywhere-get the job done scenarios, which are starting to be so fluid.
Comprehending no matter if an endpoint is dependable, tracked and recognised has a substantial influence on income. On-premises endpoint protection platforms (EPPs) really do not supply the visibility enterprises need to protected and keep endpoint configurations recent. That lack of visibility into endpoint overall health and position drains revenue.
“The on-premises deployments of endpoint protection confirmed their flaws, and one particular of the most significant flaws in this was a reduction of visibility of what’s likely on at the endpoint,” Harrington claimed.
The craze of enterprises going to internet applications, blended with document rates of convey your possess machine (BYOD) adoption, have manufactured distinct that on-premise EPP was not up to the new difficulties enterprises are facing. Below are some techniques enterprises can take on these challenges…
Go through Total Resource: VentureBeat